PowerShell’s Desired State Configuration allows for routines or classes to be run on remote machines by passing a text based “properties” object to the destination end-node. There are a growing number of Microsoft supplied “classes” and importantly, the framework allows for custom development of additional objects.
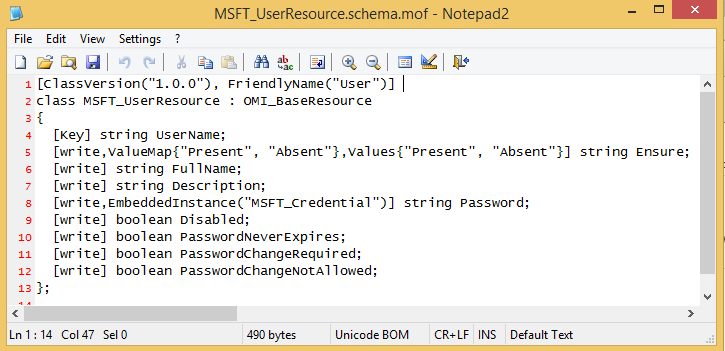
MOF Files define the inputs to the class that will be run remotely.
When DSC runs, it passes a plain text MOF file with values to a remote machine.
As the configuration file is plain text based, processes that require embedded credentials pose a major security risk. To mitigate the risk of password exposure, DSC provides an encryption mechanism to reduce the risk of passwords being divulged.
Digital Certificates
To encrypt MOF contents, we can use a digital certificate. A created certificate will hold two unique keys, one public and the other private. When two machines have copies of the same certificate, the sensitive data can be encrypted against the certificate with a Public key and unencrypted remotely by the second machine using the Private key.
For PowerShell’s DSC to utilise encryption, the first requirement is to generate a certificate. The important requirements is that the end node that receives the DSC MOF file is the machine that must unencrypt the file. To unencrypt it will be the remote machine that must hold the Private key… not the DSC serving machine.
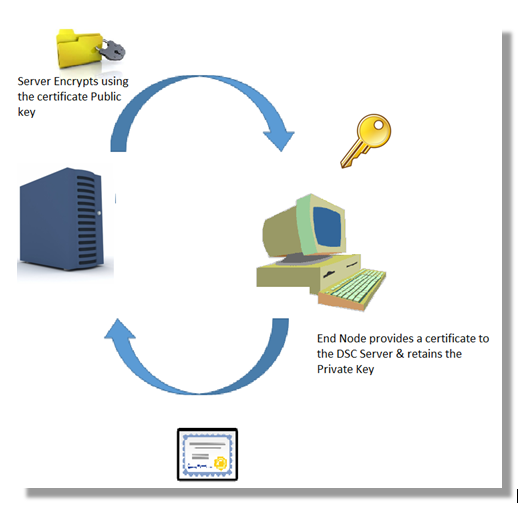
There are a couple of ways that the end node can get a certificate (and hold the Private key). An auto-enrolment policy with a certificate server might be used. In this scenario, the DSC hosting server could get a copy of the issued certificate directly from the Certificate Authority.
In other situations, a self-signed certificate might be created on the end-node specifically for encrypting credential data being passed within DSC.
Certificate Requirements
Digital certificates can be used for many types of task.
The only requirement for PowerShell DSC encryption certificate is “key agreement”.
Vadims Podans’ PowerShell based self-signed certificate generator is universally used for the task
https://gallery.technet.microsoft.com/scriptcenter/Self-signed-certificate-5920a7c6
Remember that the certificate is to be generated on the destination end-node, not the DSC issuing server. The syntax for creating a certificate in the personal store is:
[[powershell]] New-SelfSignedCertificateEx -Subject "CN=$($env:computername)" -KeyUsage "KeyAgreement" ` -StoreLocation LocalMachine -StoreName My -FriendlyName “DSC Certificate” [[/powershell]]
PowerShell DSC operates in the machine context so the command has to be run in a PowerShell session that’s opened in an Administrative context.
Certificate Stores
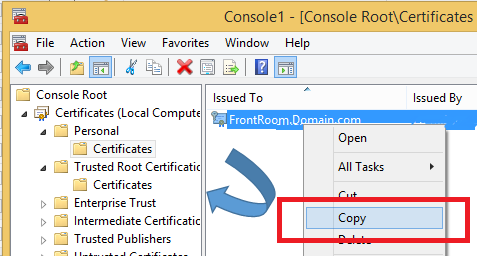
Self-Signed certificates aren’t trusted. To make the certificate usable, a copy will need to be inserted into a trusted Certificate Authority store as well.
Manually, this can be done by copy the Self-Signed certificate to the Trusted Root Certificate store.
Export the Certificate
The certificate must also be exported and copied to the DSC issuing server as it will utilise the file when encrypting DSC contents.
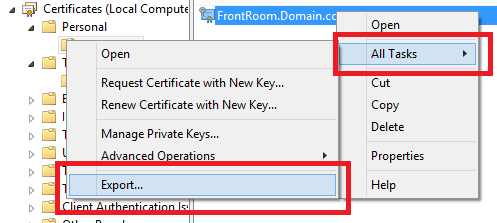

The Private key won’t be exported & DER encoding is fine.
Certificate Thumbprint
The DSC Issuing server will also need to know the thumbprint of the exported certificate.
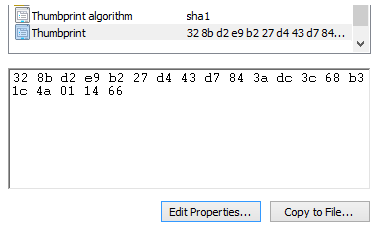
There are a couple of traps with the certificate thumbprint and PowerShell DSC. Firstly, copy and pasting the thumbprint property from a certificate uses Unicode which adds a question mark to the start of the string which isn’t always visible (depending on your text editor). The other gotcha is that the thumbprint needs to be in uppercase if DSC is going to correctly use it for decoding.
Using PowerShell to create the certificate, trust the certificate, export the certificate and report the Thumbprint is the easiest way of ensuring that your certificate requirements are met for DSC Encryption.
Automating DSC Certificate Creation
The script below uses community contributed functions from Vadims Podans, James Kehr and Wayne Martin to create DSC encryption capable certificates on test-lab machines. Its purpose is to help in getting a working test environment for used with secured PowerShell DSC. As the script accesses the Local Machine Certificate Store, it must be run elevated.
Remember that the certificate must be created on the target end-node – not the server that will issue DSC objects.
[[powershell]]
################################################################################################
#
# This script creates a self-signed certificate cable of PowerShell DSC credential encryption
# Certificate is:
#
# * added to trusted CA store
# * exported to .cer cert file
#
# Legacy certificate handling used to ensure capability with Windows Server 2008
#
# Version 0.1 23 May 2015 Laurie Rhodes
#
# *** Deserved Credit ***
#
# Primary code leveraged is from Vadims Podans
# (http://en-us.sysadmins.lv/) for certificate creation
# Certificate importing function by James Kehr
# http://www.orcsweb.com/blog/james/
# powershell-ing-on-windows-server-how-to-import-certificates-using-powershell/
# BinHex functions by Wayne Martin
# http://waynes-world-it.blogspot.com.au/
# 2008/05/binary-hex-string-files-with-powershell.html
####################################################################################>
#region Contributed Community Functions
# Contributors credited with each function
function New-SelfSignedCertificateEx {
#
#####################################################################
# New-SelfSignedCertificateEx.ps1
# Version 1.0
#
# Creates self-signed certificate. This tool is a base replacement
# for deprecated makecert.exe
#
# Vadims Podans (c) 2013
# http://en-us.sysadmins.lv/
#####################################################################
#requires -Version 2.0
.Synopsis
This cmdlet generates a self-signed certificate.
.Description
This cmdlet generates a self-signed certificate with the required data.
.Parameter Subject
Specifies the certificate subject in a X500 distinguished name format.
Example: CN=Test Cert, OU=Sandbox
.Parameter NotBefore
Specifies the date and time when the certificate become valid.
By default previous day date is used.
.Parameter NotAfter
Specifies the date and time when the certificate expires. By default,
the certificate is valid for 1 year.
.Parameter SerialNumber
Specifies the desired serial number in a hex format.
Example: 01a4ff2
.Parameter ProviderName
Specifies the Cryptography Service Provider (CSP) name. You can use
either legacy CSP and Key Storage Providers (KSP). By default
"Microsoft Enhanced Cryptographic Provider v1.0" CSP is used.
.Parameter AlgorithmName
Specifies the public key algorithm. By default RSA algorithm is used.
RSA is the only algorithm supported by legacy CSPs. With key storage
providers (KSP) you can use CNG algorithms, like ECDH. For CNG
algorithms you must use full name:
ECDH_P256
ECDH_P384
ECDH_P521
In addition, KeyLength parameter must be specified explicitly when
non-RSA algorithm is used.
.Parameter KeyLength
Specifies the key length to generate. By default 2048-bit key is
generated.
.Parameter KeySpec
Specifies the public key operations type. The possible values are:
Exchange and Signature. Default value is Exchange.
.Parameter EnhancedKeyUsage
Specifies the intended uses of the public key contained in a certificate.
You can specify either, EKU friendly name (for example
'Server Authentication') or object identifier (OID) value
(for example '1.3.6.1.5.5.7.3.1').
.Parameter KeyUsages
Specifies restrictions on the operations that can be performed
by the public key contained in the certificate.
Possible values (and their respective integer values to make
bitwise operations) are:
EncipherOnly
CrlSign
KeyCertSign
KeyAgreement
DataEncipherment
KeyEncipherment
NonRepudiation
DigitalSignature
DecipherOnly
you can combine key usages values by using bitwise OR operation.
when combining multiple flags, they must be enclosed in quotes
and separated by a comma character. For example, to combine
KeyEncipherment and DigitalSignature flags you should type:
"KeyEncipherment, DigitalSignature".
If the certificate is CA certificate (see IsCA parameter), key
usages extension is generated automatically with the following
key usages: Certificate Signing, Off-line CRL Signing, CRL Signing.
.Parameter SubjectAlternativeName
Specifies alternative names for the subject. Unlike Subject
field, this extension allows to specify more than one name.
Also, multiple types of alternative names are supported.
The cmdlet supports the following SAN types:
RFC822 Name
IP address (both, IPv4 and IPv6)
Guid
Directory name
DNS name
.Parameter IsCA
Specifies whether the certificate is CA (IsCA = $true) or
end entity (IsCA = $false) certificate. If this parameter
is set to $false, PathLength parameter is ignored.
Basic Constraints extension is marked as critical.
.PathLength
Specifies the number of additional CA certificates in the
chain under this certificate. If PathLength parameter is
set to zero, then no additional (subordinate) CA certificates
are permitted under this CA.
.CustomExtension
Specifies the custom extension to include to a self-signed
certificate. This parameter must not be used to specify the
extension that is supported via other parameters. In order
to use this parameter, the extension must be formed in a
collection of initialized
System.Security.Cryptography.X509Certificates.X509Extension
objects.
.Parameter SignatureAlgorithm
Specifies signature algorithm used to sign the certificate.
By default 'SHA1' algorithm is used.
.Parameter FriendlyName
Specifies friendly name for the certificate.
.Parameter StoreLocation
Specifies the store location to store self-signed certificate.
Possible values are: 'CurrentUser' and 'LocalMachine'. 'CurrentUser'
store is intended for user certificates and computer (as well as CA)
certificates must be stored in 'LocalMachine' store.
.Parameter StoreName
Specifies the container name in the certificate store.
Possible container names are:
AddressBook
AuthRoot
CertificateAuthority
Disallowed
My
Root
TrustedPeople
TrustedPublisher
.Parameter Path
Specifies the path to a PFX file to export a self-signed certificate.
.Parameter Password
Specifies the password for PFX file.
.Parameter AllowSMIME
Enables Secure/Multipurpose Internet Mail Extensions for the certificate.
.Parameter Exportable
Marks private key as exportable. Smart card providers usually do not allow
exportable keys.
.Example
New-SelfsignedCertificateEx -Subject "CN=Test Code Signing"
-EKU "Code Signing" -KeySpec "Signature" `
-KeyUsage "DigitalSignature" -FriendlyName "Test code signing" -NotAfter [datetime]::now.AddYears(5)
Creates a self-signed certificate intended for code signing and which
is valid for 5 years
. Certificate
is saved in the Personal store of the current user account.
.Example
New-SelfsignedCertificateEx -Subject "CN=www.domain.com" `
-EKU "Server Authentication", "Client authentication" `
-KeyUsage "KeyEcipherment, DigitalSignature" -SAN "sub.domain.com","www.domain.com","192.168.1.1" `
-AllowSMIME -Path C:\test\ssl.pfx `
-Password (ConvertTo-SecureString "P@ssw0rd" -AsPlainText -Force) `
-Exportable `
-StoreLocation "LocalMachine"
Creates a self-signed SSL certificate with multiple subject names and
saves it to a file. Additionally, the certificate is saved in the
Personal store of the Local Machine store. Private key is marked as
exportable, so you can export the certificate with a associated private
key to a file at any time. The certificate includes SMIME capabilities.
.Example
New-SelfsignedCertificateEx -Subject "CN=www.domain.com" `
-EKU "Server Authentication", "Client authentication" `
-KeyUsage "KeyEcipherment, DigitalSignature" -SAN "sub.domain.com","www.domain.com","192.168.1.1" `
-StoreLocation "LocalMachine" `
-ProviderName "Microsoft Software Key Storae Provider" -AlgorithmName ecdh_256 `
-KeyLength 256 -SignatureAlgorithm sha256
Creates a self-signed SSL certificate with multiple subject names and
saves it to a file. Additionally, the certificate is saved in the
Personal store of the Local Machine store. Private key is marked as exportable,
so you can export the certificate with a associated private key to a
file at any time. Certificate uses
Ellyptic Curve Cryptography (ECC) key algorithm ECDH with 256-bit key.
The certificate is signed by using SHA256 algorithm.
.Example
New-SelfsignedCertificateEx -Subject "CN=Test Root CA, OU=Sandbox" `
-IsCA $true -ProviderName `
"Microsoft Software Key Storage Provider" -Exportable
Creates self-signed root CA certificate.
#>
[CmdletBinding(DefaultParameterSetName = '__store')]
param (
[Parameter(Mandatory = $true, Position = 0)]
[string]$Subject,
[Parameter(Position = 1)]
[datetime]$NotBefore = [DateTime]::Now.AddDays(-1),
[Parameter(Position = 2)]
[datetime]$NotAfter = $NotBefore.AddDays(365),
[string]$SerialNumber,
[Alias('CSP')]
[string]$ProviderName = "Microsoft Enhanced Cryptographic Provider v1.0",
[string]$AlgorithmName = "RSA",
[int]$KeyLength = 2048,
[validateSet("Exchange","Signature")]
[string]$KeySpec = "Exchange",
[Alias('EKU')]
[Security.Cryptography.Oid[]]$EnhancedKeyUsage,
[Alias('KU')]
[Security.Cryptography.X509Certificates.X509KeyUsageFlags]$KeyUsage,
[Alias('SAN')]
[String[]]$SubjectAlternativeName,
[bool]$IsCA,
[int]$PathLength = -1,
[Security.Cryptography.X509Certificates.X509ExtensionCollection]$CustomExtension,
[ValidateSet('MD5','SHA1','SHA256','SHA384','SHA512')]
[string]$SignatureAlgorithm = "SHA1",
[string]$FriendlyName,
[Parameter(ParameterSetName = '__store')]
[Security.Cryptography.X509Certificates.StoreLocation]$StoreLocation = "CurrentUser",
[Parameter(ParameterSetName = '__store')]
[Security.Cryptography.X509Certificates.StoreName]$StoreName = "My",
[Parameter(Mandatory = $true, ParameterSetName = '__file')]
[Alias('OutFile','OutPath','Out')]
[IO.FileInfo]$Path,
[Parameter(Mandatory = $true, ParameterSetName = '__file')]
[Security.SecureString]$Password,
[switch]$AllowSMIME,
[switch]$Exportable
)
$ErrorActionPreference = "Stop"
if ([Environment]::OSVersion.Version.Major -lt 6) {
$NotSupported = New-Object NotSupportedException `
-ArgumentList "Windows XP and Windows Server 2003 are not supported!"
throw $NotSupported
}
$ExtensionsToAdd = @()
#region constants
# contexts
New-Variable -Name UserContext -Value 0x1 -Option Constant
New-Variable -Name MachineContext -Value 0x2 -Option Constant
# encoding
New-Variable -Name Base64Header -Value 0x0 -Option Constant
New-Variable -Name Base64 -Value 0x1 -Option Constant
New-Variable -Name Binary -Value 0x3 -Option Constant
New-Variable -Name Base64RequestHeader -Value 0x4 -Option Constant
# SANs
New-Variable -Name OtherName -Value 0x1 -Option Constant
New-Variable -Name RFC822Name -Value 0x2 -Option Constant
New-Variable -Name DNSName -Value 0x3 -Option Constant
New-Variable -Name DirectoryName -Value 0x5 -Option Constant
New-Variable -Name URL -Value 0x7 -Option Constant
New-Variable -Name IPAddress -Value 0x8 -Option Constant
New-Variable -Name RegisteredID -Value 0x9 -Option Constant
New-Variable -Name Guid -Value 0xa -Option Constant
New-Variable -Name UPN -Value 0xb -Option Constant
# installation options
New-Variable -Name AllowNone -Value 0x0 -Option Constant
New-Variable -Name AllowNoOutstandingRequest -Value 0x1 -Option Constant
New-Variable -Name AllowUntrustedCertificate -Value 0x2 -Option Constant
New-Variable -Name AllowUntrustedRoot -Value 0x4 -Option Constant
# PFX export options
New-Variable -Name PFXExportEEOnly -Value 0x0 -Option Constant
New-Variable -Name PFXExportChainNoRoot -Value 0x1 -Option Constant
New-Variable -Name PFXExportChainWithRoot -Value 0x2 -Option Constant
#endregion
#region Subject processing
# http://msdn.microsoft.com/en-us/library/aa377051(VS.85).aspx
$SubjectDN = New-Object -ComObject X509Enrollment.CX500DistinguishedName
$SubjectDN.Encode($Subject, 0x0)
#endregion
#region Extensions
#region Enhanced Key Usages processing
if ($EnhancedKeyUsage) {
$OIDs = New-Object -ComObject X509Enrollment.CObjectIDs
$EnhancedKeyUsage | %{
$OID = New-Object -ComObject X509Enrollment.CObjectID
$OID.InitializeFromValue($_.Value)
# http://msdn.microsoft.com/en-us/library/aa376785(VS.85).aspx
$OIDs.Add($OID)
}
# http://msdn.microsoft.com/en-us/library/aa378132(VS.85).aspx
$EKU = New-Object -ComObject X509Enrollment.CX509ExtensionEnhancedKeyUsage
$EKU.InitializeEncode($OIDs)
$ExtensionsToAdd += "EKU"
}
#endregion
#region Key Usages processing
if ($KeyUsage -ne $null) {
$KU = New-Object -ComObject X509Enrollment.CX509ExtensionKeyUsage
$KU.InitializeEncode([int]$KeyUsage)
$KU.Critical = $true
$ExtensionsToAdd += "KU"
}
#endregion
#region Basic Constraints processing
if ($PSBoundParameters.Keys.Contains("IsCA")) {
# http://msdn.microsoft.com/en-us/library/aa378108(v=vs.85).aspx
$BasicConstraints = New-Object -ComObject X509Enrollment.CX509ExtensionBasicConstraints
if (!$IsCA) {$PathLength = -1}
$BasicConstraints.InitializeEncode($IsCA,$PathLength)
$BasicConstraints.Critical = $IsCA
$ExtensionsToAdd += "BasicConstraints"
}
#endregion
#region SAN processing
if ($SubjectAlternativeName) {
$SAN = New-Object -ComObject X509Enrollment.CX509ExtensionAlternativeNames
$Names = New-Object -ComObject X509Enrollment.CAlternativeNames
foreach ($altname in $SubjectAlternativeName) {
$Name = New-Object -ComObject X509Enrollment.CAlternativeName
if ($altname.Contains("@")) {
$Name.InitializeFromString($RFC822Name,$altname)
} else {
try {
$Bytes = [Net.IPAddress]::Parse($altname).GetAddressBytes()
$Name.InitializeFromRawData($IPAddress,$Base64,[Convert]::ToBase64String($Bytes))
} catch {
try {
$Bytes = [Guid]::Parse($altname).ToByteArray()
$Name.InitializeFromRawData($Guid,$Base64,[Convert]::ToBase64String($Bytes))
} catch {
try {
$Bytes = ([Security.Cryptography.X509Certificates.X500DistinguishedName]$altname).RawData
$Name.InitializeFromRawData($DirectoryName,$Base64,[Convert]::ToBase64String($Bytes))
} catch {$Name.InitializeFromString($DNSName,$altname)}
}
}
}
$Names.Add($Name)
}
$SAN.InitializeEncode($Names)
$ExtensionsToAdd += "SAN"
}
#endregion
#region Custom Extensions
if ($CustomExtension) {
$count = 0
foreach ($ext in $CustomExtension) {
# http://msdn.microsoft.com/en-us/library/aa378077(v=vs.85).aspx
$Extension = New-Object -ComObject X509Enrollment.CX509Extension
$EOID = New-Object -ComObject X509Enrollment.CObjectId
$EOID.InitializeFromValue($ext.Oid.Value)
$EValue = [Convert]::ToBase64String($ext.RawData)
$Extension.Initialize($EOID,$Base64,$EValue)
$Extension.Critical = $ext.Critical
New-Variable -Name ("ext" + $count) -Value $Extension
$ExtensionsToAdd += ("ext" + $count)
$count++
}
}
#endregion
#endregion
#region Private Key
# http://msdn.microsoft.com/en-us/library/aa378921(VS.85).aspx
$PrivateKey = New-Object -ComObject X509Enrollment.CX509PrivateKey
$PrivateKey.ProviderName = $ProviderName
$AlgID = New-Object -ComObject X509Enrollment.CObjectId
$AlgID.InitializeFromValue(([Security.Cryptography.Oid]$AlgorithmName).Value)
$PrivateKey.Algorithm = $AlgID
# http://msdn.microsoft.com/en-us/library/aa379409(VS.85).aspx
$PrivateKey.KeySpec = switch ($KeySpec) {"Exchange" {1}; "Signature" {2}}
$PrivateKey.Length = $KeyLength
# key will be stored in current user certificate store
switch ($PSCmdlet.ParameterSetName) {
'__store' {
$PrivateKey.MachineContext = if ($StoreLocation -eq "LocalMachine") {$true} else {$false}
}
'__file' {
$PrivateKey.MachineContext = $false
}
}
$PrivateKey.ExportPolicy = if ($Exportable) {1} else {0}
$PrivateKey.Create()
#endregion
# http://msdn.microsoft.com/en-us/library/aa377124(VS.85).aspx
$Cert = New-Object -ComObject X509Enrollment.CX509CertificateRequestCertificate
if ($PrivateKey.MachineContext) {
$Cert.InitializeFromPrivateKey($MachineContext,$PrivateKey,"")
} else {
$Cert.InitializeFromPrivateKey($UserContext,$PrivateKey,"")
}
$Cert.Subject = $SubjectDN
$Cert.Issuer = $Cert.Subject
$Cert.NotBefore = $NotBefore
$Cert.NotAfter = $NotAfter
foreach ($item in $ExtensionsToAdd) {$Cert.X509Extensions.Add((Get-Variable -Name $item -ValueOnly))}
if (![string]::IsNullOrEmpty($SerialNumber)) {
if ($SerialNumber -match "[^0-9a-fA-F]") {throw "Invalid serial number specified."}
if ($SerialNumber.Length % 2) {$SerialNumber = "0" + $SerialNumber}
$Bytes = $SerialNumber -split "(.{2})" | ?{$_} | %{[Convert]::ToByte($_,16)}
$ByteString = [Convert]::ToBase64String($Bytes)
$Cert.SerialNumber.InvokeSet($ByteString,1)
}
if ($AllowSMIME) {$Cert.SmimeCapabilities = $true}
$SigOID = New-Object -ComObject X509Enrollment.CObjectId
$SigOID.InitializeFromValue(([Security.Cryptography.Oid]$SignatureAlgorithm).Value)
$Cert.SignatureInformation.HashAlgorithm = $SigOID
# completing certificate request template building
$Cert.Encode()
# interface: http://msdn.microsoft.com/en-us/library/aa377809(VS.85).aspx
$Request = New-Object -ComObject X509Enrollment.CX509enrollment
$Request.InitializeFromRequest($Cert)
$Request.CertificateFriendlyName = $FriendlyName
$endCert = $Request.CreateRequest($Base64)
$Request.InstallResponse($AllowUntrustedCertificate,$endCert,$Base64,"")
switch ($PSCmdlet.ParameterSetName) {
'__file' {
$PFXString = $Request.CreatePFX(
[Runtime.InteropServices.Marshal]::PtrToStringAuto([Runtime.InteropServices.Marshal]::SecureStringToBSTR($Password)),
$PFXExportEEOnly,
$Base64
)
Set-Content -Path $Path -Value ([Convert]::FromBase64String($PFXString)) -Encoding Byte
}
}
}
#########################################################################################
# Import-509Certificate ([string]$certPath , [string]certRootStore , [string]$certStore)
# Function by James Kehr
# http://www.orcsweb.com/blog/
# james/powershell-ing-on-windows-server-how-to-import-certificates-using-powershell/
#
#########################################################################################>
function Import-509Certificate {
param([String]$certPath,[String]$certRootStore,[String]$certStore)
$pfx = new-object System.Security.Cryptography.X509Certificates.X509Certificate2
$pfx.import($certPath)
$store = new-object System.Security.Cryptography.X509Certificates.X509Store($certStore,$certRootStore)
$store.open(“MaxAllowed”)
$store.add($pfx)
$store.close()
}
##############################################################################################
# HexStringToBinary ([string]$Hex , [string]$OutputFile)
# Function by Wayne Martin
# http://waynes-world-it.blogspot.com.au
# /2008/05/binary-hex-string-files-with-powershell.html
#
# Writes a Hex string back to a binary format.
###############################################################################################>
function HexStringToBinary{
param(
[Parameter(Mandatory = $true)]
[string] $HexString = "",
[Parameter(Mandatory = $true)]
[string] $OutputFile = ""
)
if ($Hexstring -ne "") {
#$HexString = Get-Content -readcount 0 -path $HexStringinput
#$HexString = $HexString[0]
$count = $hexString.length
$byteCount = $count/2
$bytes = New-Object byte[] $byteCount
$byte = $null
$x = 0
for ( $i = 0; $i -le $count-1; $i+=2 )
{
$bytes[$x] = [byte]::Parse($hexString.Substring($i,2), [System.Globalization.NumberStyles]::HexNumber)
$x += 1
}
if ($OutputFile -ne "") {
set-content -encoding byte $OutputFile -value $bytes
} else {
write-error "No output file specified"
}
} else{
write-error "Error, no input file specified"
}
# Byte.Parse Method (String, NumberStyles)
# http://msdn.microsoft.com/en-us/library/4eszwye3(VS.80).aspx
}
##############################################################################
# BinaryToHexString([string]$PathtoBinaryfile)
# Function by Wayne Martin
# http://waynes-world-it.blogspot.com.au
# /2008/05/binary-hex-string-files-with-powershell.html
#
# Writes a Hex string back to a binary format.
#############################################################################>
function BinaryToHexString{
param(
[Parameter(Mandatory = $true)]
[string] $Binaryfile = ""
)
if ($BinaryFile -ne "") {
[byte[]]$bytes = Get-Content -encoding byte -readcount 0 -path $BinaryFile
# Use a readCount of 0 to read all lines at once
$output = new-object System.Text.StringBuilder
# Using stringBuilder seems faster than $a = $a + "a" ?
$count = $bytes.length # The loop seems much faster when using a pre-set value?
for ($i = 0; $i -le $count-1; $i++)
{
$hex = "{0:x}" -f $bytes[$i]
[void]$output.Append($hex.PadLeft(2, "0")) # Pad any single digits
}
return $output.ToString()
} else{
write-host "Error, no input file specified"
}
}
#endregion
##############################################################################
# New-DSC ([string]$FriendlyName)
#
# Creates a self-signed cerificate for use with PowerShell DSC
# FriendlyName is mandatory & is used for tagging the created
# certificates so they may be easily identified for
# removal at a later time
##############################################################################>
function New-DSCCert(){
param (
# Create a Unique Friendly Name tag
[Parameter(Mandatory = $true)]
[ValidateNotNullorEmpty()]
[string]$FriendlyName
)
# The File location for the exported Certificate
$ExportCertFile = "$($env:TEMP)\$($env:computername).cer"
If (-NOT ([Security.Principal.WindowsPrincipal] [Security.Principal.WindowsIdentity]::GetCurrent()).IsInRole(`
[Security.Principal.WindowsBuiltInRole] "Administrator"))
{
Write-Warning "Script must be run with Admin Privileges"
Break
}
New-SelfSignedCertificateEx -Subject "CN=$($env:computername)" -KeyUsage "KeyAgreement" `
-StoreLocation LocalMachine -StoreName My -FriendlyName $FriendlyName
# Create a handle to the certificate
# Note that multiple certificates with the same friendly name could be returned
# We will assume the desired certificate is the first in the returned array
$foundCertArray = get-childitem cert:\LocalMachine\My | where-object {$_.FriendlyName -eq $FriendlyName }
#Export the Certificate - can't rely upon 'Export-Certificate' being available
"Exporting Certificate $($foundCertArray[0].Thumbprint)"
If (Test-Path $ExportCertFile){ Remove-Item $ExportCertFile }
[byte[]]$Bytes = $foundCertArray[0].Export('Cert')
[io.file]::WriteAllBytes($ExportCertFile,$Bytes)
# Re-import to the trusted root store using James Kehr's function
# this enables the trust
#re-import to the trusted root store using James Kehr's function
Import-509Certificate $ExportCertFile “LocalMachine” “AuthRoot”
# Add friendly name on Imported Root CA so queries against the name
# can be used to clean up at a later time.
$RootCA = get-childitem Cert:\LocalMachine\AuthRoot | where-object {$_.Thumbprint -eq $foundCertArray[0].Thumbprint }
$RootCA[0].FriendlyName = $($FriendlyName)
Write-Debug "CA Trusted Thumbprint = $($RootCA[0].Thumbprint)"
Start-Process -FilePath "C:\Windows\Explorer.exe" -ArgumentList "$($env:TEMP)"
}
#### Call the example script
cls
New-DSCCert "PowerShell DSC"
[[/powershell]]
- Log in to post comments